Audit Incoming Call Records – 2122795139, 8642147240, 5673580647, 4699988648, 4787427582, 5157353419, 9029123279, 8023301033, 5143940805, 5753290604
An audit-focused examination of the ten listed call numbers will model meticulous metadata capture, normalization to a unified schema, and anomaly assessment against established baselines. The approach remains skeptical, documenting uncertainties and corroborating findings across data fragments. It aims to define controls, governance actions, and traceability, all while aligning with regulatory expectations. The discussion will identify risk signals and potential gaps, yet stops short of conclusions, inviting further scrutiny and validation before implementation.
What Audit-Wocused Call Logs Reveal About Risk and Compliance
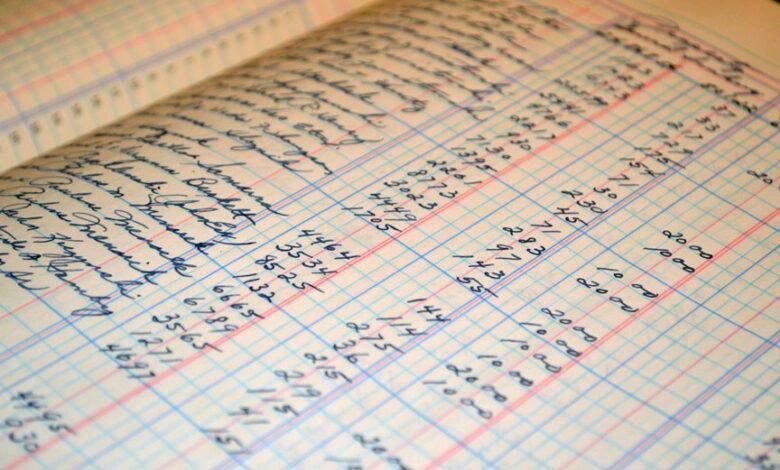
Audit-focused call logs offer a granular view of organizational risk and compliance posture by capturing metadata such as caller identity, timestamps, duration, and routing paths.
The analysis remains methodical and skeptical, identifying patterns that reveal Audit findings and potential Compliance gaps.
This detached assessment prioritizes clarity over superstition, highlighting actionable insights while resisting speculative narratives about freedom without accountability.
A Step-by-Step Framework for Inspecting the 10-Phone-Number Call List
To inspect a 10-phone-number call list systematically, a step-by-step framework begins with data collection, ensuring each entry includes caller ID, timestamp, duration, call direction, and routing path, followed by normalization to a common format.
The process emphasizes data integrity, rigorous documentation, and regulatory alignment, applying skeptical verification, reproducible methods, and disciplined auditing for freedom-minded oversight.
Detecting Anomalies: Patterns That Signal Quality Gaps and Fraud
Detecting anomalies requires a disciplined, evidence-driven approach that distinguishes genuine variability from systemic faults and intentional deception.
The analysis identifies anomaly signals that repeatedly diverge from baseline patterns, flagging potential quality gaps and fraud indicators.
Methodically, teams compare expected versus observed behaviors, test hypotheses, and document uncertainties, maintaining skepticism about outliers while seeking reproducible corroboration across datasets.
Translating Findings Into Controls, Savings, and Governance Actions
This phase translates the insights from anomaly detection in incoming call records into concrete controls, concrete savings opportunities, and governance actions. The analysis converts findings into actionable measures, balancing risk and cost.
It identifies compliance gaps and articulates governance actions, ensuring accountability, traceability, and ongoing monitoring. Skeptical scrutiny prevents overclaiming, while disciplined implementation enables measurable, sustainable improvements without stifling operational freedom.
Conclusion
This audit applies a disciplined, skeptical lens to each inbound record, tracing metadata, normalization, and routing paths with meticulous care. Patterns are weighed against baselines, uncertainties are documented, and corroboration across datasets is pursued. As anomalies emerge, the findings point to control gaps and governance needs, yet the truth remains provisional until cross-checks resolve ambiguities. In the quiet margins of the logs, the stakes—compliance, traceability, and ongoing monitoring—hint at consequences that could redefine risk posture. The clock ticks.





